How to spot a phishing email
How to catch a phish
The six signs of a suspicious email
Cybercriminals use phishing emails to manipulate people into doing what they want, including providing personal information such as banking or identification records. Because of this element of manipulating human emotions, phishing is considered a kind of social engineering.
Technology makes manipulation through phishing easy. Setting up and operating a phishing attack is fast, inexpensive and low risk: any cybercriminal with an email address can launch one.
According to Verizon’s 2017 Data Breach Investigations Report, the education sector saw a rise in social engineering–based attacks. Students, staff, and faculty all lose when personal data and research are disclosed to unauthorized parties.
Phishing played a part in more than 40 per cent of these breaches. Knowing what you’re up against can help you be more secure in your online life.
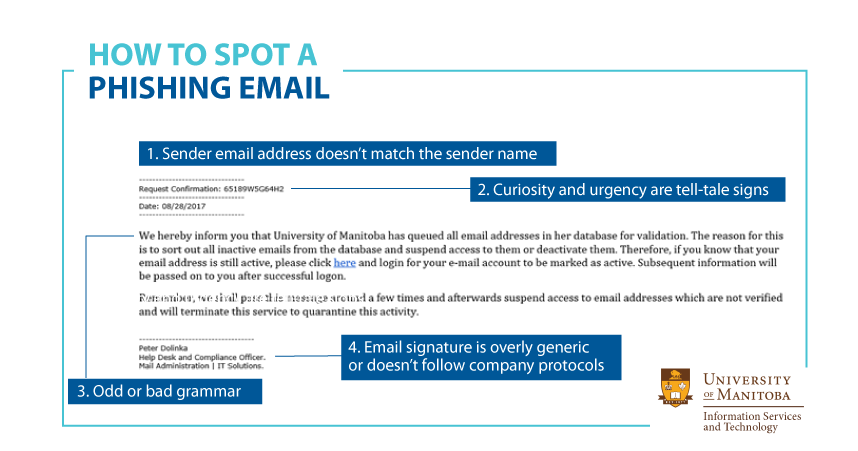
Here are the six signs of a suspicious email:
- Stranger danger: A sender address that does not match the sender name
- No John Hancock: A signature that is overly generic
- Hover to discover: Mouse over links in email to reveal their true URL. If the name and the URL do not match, delete the email.
- Do not open unexpected attachments: They are a cybercriminal’s #1 choice for spreading malicious software.
- Trust your instincts: Does that email feel ‘off’ in some way? It probably is. Forward it to spam[at]umanitoba[dot]ca to confirm the message.
- Is it urgent? Slow down. An “IMPORTANT MESSAGE” may be a phishing attempt. Cybercriminals want you to do what you’re told, when you’re told. Think before you click.
If an email you’ve received contains two or more of the indicators listed above, delete it or forward the message to spam[at]umanitoba[dot]ca.
For more information about phishing attacks, visit the Information Security and Compliance web page at http://umanitoba.ca/computing/ist/security/phishing.html.